11 hidden apnscp tricks
Hidden API commands in apnscp that help you achieve more from the command-line.

apnscp has plenty of gems hidden throughout its code. Some features unarguably more helpful than others. Here is part one of a two part installment covering 11 unsung heroes that'll provide enough value to arouse your curiosity!
All commands can be interacted with from the control panel or command-line.
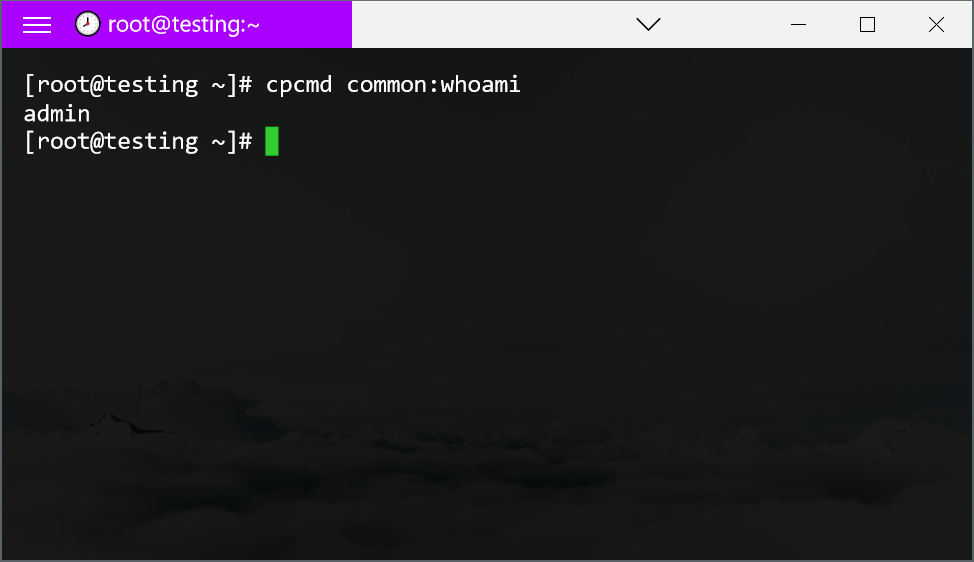
Command-line: cpcmd method:name arg1 arg2
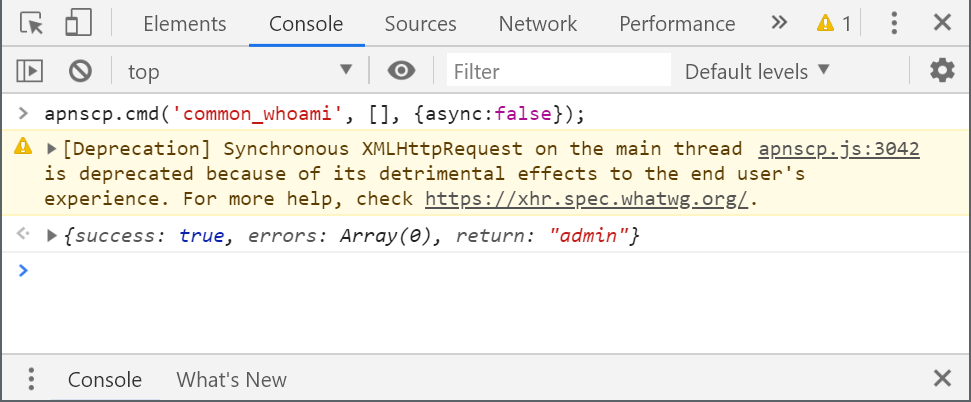
Control panel (JavaScript console - F12): apnscp.cmd('method_name', ['arg1','arg2'], {async: false});
Note that CLI supports alternative invocation, i.e. module_method_name can be written as module:method-name. SOAP API and browser interactions do not support this. For clarity, alternative invocation is used.
- letsencrypt:append array $names, bool $verifyip = true
Unlike letsencrypt:request, append does not replace the certificate with members with the named set. $verifyip confirms the IP address matches the account before proceeding. Disable if behind a proxy such as CloudFlare.
Example:cpcmd -d domain.com letsencrypt:append '[newdomain.com,www.newdomain.com]' - rampart:whitelist string $ip, string $mode = 'add'
Whitelisting grants brute-force immunity to the specified IP address. Specify 'remove' as $mode to remove the entry.
Example:apnscp.cmd('rampart_whitelist', ['64.22.68.1'], {async: false}); - admin:locate-webapps array $sites = null
Scour all sites or just the sites specified in $specifier for known webapps. Any detected apps will be associated with the account.
Example:cpcmd admin:locate-webapps '[site12,mydomain.com,site1]' - admin:update-webapps array $specifier = null
A complementary method to locate-webapps, update-webapps will perform an update on the set of known apps that matches the specified criteria (mutually inclusive).
Example:apnscp.cmd('admin_update_webapps', {'type': 'ghost'}, {async: false}); - admin:reset-webapp-failure array $specifier = null
Reset all failures across one or more sites. $specifier is an inclusive list of site, type, and version. For example, if WordPress 5.1.2 to 5.2.0 was a bad update for all, specify type: wordpress and version: 5.1.2.
Example:cpcmd admin:reset-webapp-failure '[site:mydomain.com,type:drupal]' - rampart:blacklist string $ip, string $mode = 'add'
Another complementary method, this works similar to rampart:whitelist except that it drops any packets from the specified IP address or range to the server, useful if for example you need to block a range of countries from accessing a server. blacklist works great with country bans too, just feed it a list as input from IPdeny:
curl -o- http://www.ipdeny.com/ipblocks/data/countries/cn.zone | while read -r IP ; do cpcmd rampart:blacklist "$IP" ; done - rampart:ban string $ip, string $jail
A sibling method with a few differences: (1) ban rejects the packet indicating the machine actively denied the request, (2) has an expiry (10 days if jail is "recidive"), (3) users may also unban themselves from the service if their IP address matches the banned IP.
Example:apnscp.cmd('rampart_blacklist', ['103.89.228.0/22'], {async: false }); - config:list
config:list is part of a broader, powerful set of system abstraction called Scopes. Scopes allow you to quickly reconfigure a server in a structured, fail-safe way. config:list lists all known Scopes.config:info,config:setandconfig:getare accessory helpers to this. Important scopes are covered in the apnscp Cheatsheet.
Example:cpcmd config:list - file:audit string $path, array $requirements = [], bool $union = true
audit is an accessory method to Fortification, which is a security feature that places the web user for PHP applications under a separate UID than the account holder. Running audit on an account generates a list of matching files for further inspection, such as files created by the web server or have permissions that allow write-access by the web server. $requirements is a set user, perm, mtime, ctime, regex, and name options passed directly to find(1). $union affects whether requirements are mutually inclusive or independent.
Example:apnscp.cmd('file_audit', ['/var/www/html',{user: 'apache', perm: 666}, false], {async: false}); - common:load-preferences string $user = null
Preferences are user-specific settings, including panel settings and known web apps. This can be mixed with -d domain or -u user incpcmdto get preferences for the primary account holder or a secondary user on a domain. Specifying both -d and -u to cpcmd would be the same as cpcmd -d domain common:load-preferences user.
Example:cpcmd -d mydomain.com common:load-preferences
Protip: On apnscp 3.1+, specify yaml or json as the output format for easy readability/piping.
Example:cpcmd -d mydomain.com -u newuser -o yaml common:load-preferences - misc:list-commands
Display all commands available to the user. With apnscp 3.1 and cpcmd use -o yaml to improve readability. Every role has different commands, try them out with everyone!
Example:apnscp.cmd('misc_list_commands', [], {async: false});